At the world’s biggest real-time cyber security exercise, it’s not the winning but the taking part that counts.
Organised by the Tallinn-based NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE), Locked Shields has been running since 2010. This year, representatives from 30 nations, including from as far away as Australia and Japan, are taking part. Around 1,500 participants from the military and private sector are involved in the exercise, running from 8 to 12 April.
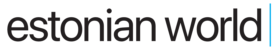
The exercise is a unique two-day opportunity for national cyber experts to practice protection of national IT systems and critical infrastructure under the pressure of a severe cyberattack. The scenario sees a Red Team fight against a Blue Team for control of the fictional island of Berylia. The Red Team, which represents the fictional nation of Crimsonia, is based in Tallinn, but the blue teams, acting as national rapid reaction teams, are situated in their home countries and will use their skills to try and win. This year, 23 blue teams are taking part.
A fictional Berylia experiencing a deteriorating security situation
While Locked Shields is a competition, the most important aspect is that each team completes the exercise knowing more than when they started.
“We will only announce the top three and the rest of the teams will be anonymous,” said the director of the CCDCOE, Colonel Jaak Tarien. “We want the teams to experiment and learn. Nobody needs to be ashamed if they bring a new team to this exercise [and they fail]. For us, the focus is to provide the best training available.”
The technology branch head of the CCDCOE, Raimo Peterson, reiterated this message. “The point is its not to win, and I’m always underlining that. The target is to have the highest learning curve.”
This year’s scenario sees the fictional Atlantic island Berylia, a NATO member, experiencing a deteriorating security situation. A number of hostile events are coinciding with coordinated cyberattacks against a major civilian internet service provider and military airbase. The attacks are causing severe disruptions in the operations of the electric power grid, 4G public safety networks, drone operation and other critical infrastructure components.
This is where the 23 blue teams come in to support the government of Berylia. Locked Shields tests how the nations would use their cyber strategies to collaborate with foreign governments to deter and recover from a cyberattack. In addition to maintaining complex IT systems, the blue teams must be effective in reporting incidents, executing strategic decisions and solving forensic, legal and media challenges. The simulation takes place 23 times – one for each team – on the NATO cyber range in Tallinn.
Making the exercise true to life
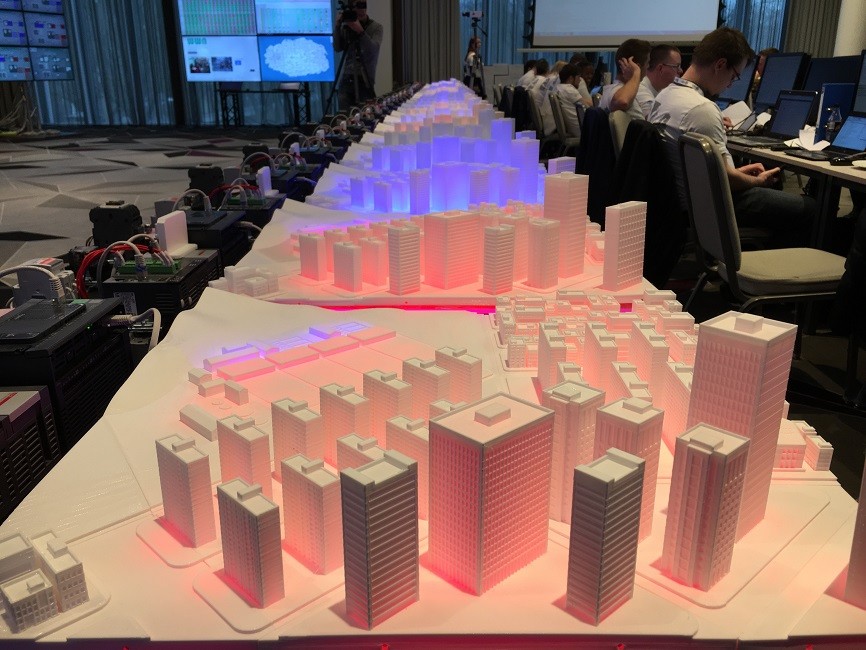
At the Hilton Hotel, in the middle of the afternoon on the first day, groups of people wearing yellow, green and white T-shirts sit at rows of tables in front of computers overseeing the exercise as it takes place. On the walls, computer screens display the scoreboard for the 23 teams, maps of Berylia and mock-ups of critical infrastructure including a power grid and water plant. Next door, the Red Team is carrying out its attacks.
What makes Locked Shields unique is the inclusion of the private sector to make the exercise true to life. The infrastructure systems the teams are fighting to control are replicas of the real systems companies have in place, rather than a complete simulation. The power grids, water plants and 4G networks under attack are mock-ups of the real thing. But it wasn’t always this way. When Locked Shields first started, the exercise used entirely fictional infrastructure. Raimo Peterson told Estonian World that getting the companies involved took some persuading at the beginning.
“There was resistance because the private sector companies were a little bit afraid about the publicity if we were hacking their systems,” Peterson, who was acting as head of the Green team, said. “But the objective of this exercise is to teach people to configure the systems safely and securely. We are not testing products.”
Although Peterson did admit that, on some occasions, the teams have accidentally detected flaws in the companies’ IT systems. This information was then passed discretely back to the company so it can fix its weak spots.
The benefit of having the private sector involved is that it improves everyone’s knowledge of what could happen, and how nations and governments would react, if a cyberattack on critical infrastructure does occur in the future. “Our interest is to have them onboard in order to build more realistic environments and their interest is that people around the world can operate their systems securely if a crisis does happen,” Peterson said.
Helping allies work closely together
Talking about the evolution of Locked Shields, the exercise director of the CCDCOE, Lauri Luht, said the competition had grown “significantly” over the last nine years, adding more challenges and with more teams signing up to participate. This year there is an emphasis on teams working together. For the first time, the blue teams have the opportunity to share information with other groups, rather than just among themselves. “It’s not only about competition – it is about collaboration and helping our allies and partners to work closely together,” he noted.
Locked Shields 2019 is organised by the NATO Cooperative Cyber Defence Centre of Excellence in cooperation with the Estonian Defence Forces, the Finnish Defence Forces, the United States European Command, the National Security Research Institute of the Republic of Korea and the Tallinn University of Technology.
Industry partners in the exercise include Siemens, Elisa, Cybernetica, Cisco, VTT Technical Research Centre of Finland, Arctic Security, Clarified Security, Iptron, Bytelife, BHC Laboratory, Bolt and many others.
I
Cover image by Helen Wright. Images courtesy of the NATO Cooperative Cyber Defence Centre of Excellence and Helen Wright.